192.168.40.116 机器上
ip a
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
|
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens192: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc mq state UP group default qlen 1000
link/ether 00:0c:29:94:5c:7f brd ff:ff:ff:ff:ff:ff
inet 192.168.40.116/24 brd 192.168.40.255 scope global noprefixroute ens192
valid_lft forever preferred_lft forever
inet 172.17.10.10/24 scope global ens192
valid_lft forever preferred_lft forever
inet6 2408:8606:8400:30a:6::41/128 scope global noprefixroute dynamic
valid_lft 6018sec preferred_lft 5718sec
inet6 fe80::d6f6:f5f6:1e6c:cf29/64 scope link noprefixroute
valid_lft forever preferred_lft forever
3: virbr0: <NO-CARRIER,BROADCAST,MULTICAST,UP> mtu 1500 qdisc noqueue state DOWN group default qlen 1000
link/ether 52:54:00:26:ce:e5 brd ff:ff:ff:ff:ff:ff
inet 192.168.122.1/24 brd 192.168.122.255 scope global virbr0
valid_lft forever preferred_lft forever
|
ens192 为默认网卡
sudo tcpdump ‘port 9000’ -w a.cap -i ens192
监听 9000 端口 上的请求,指定 网卡 为 ens192 并将其保存到 a.cap 文件中
下载 a.cap 文件
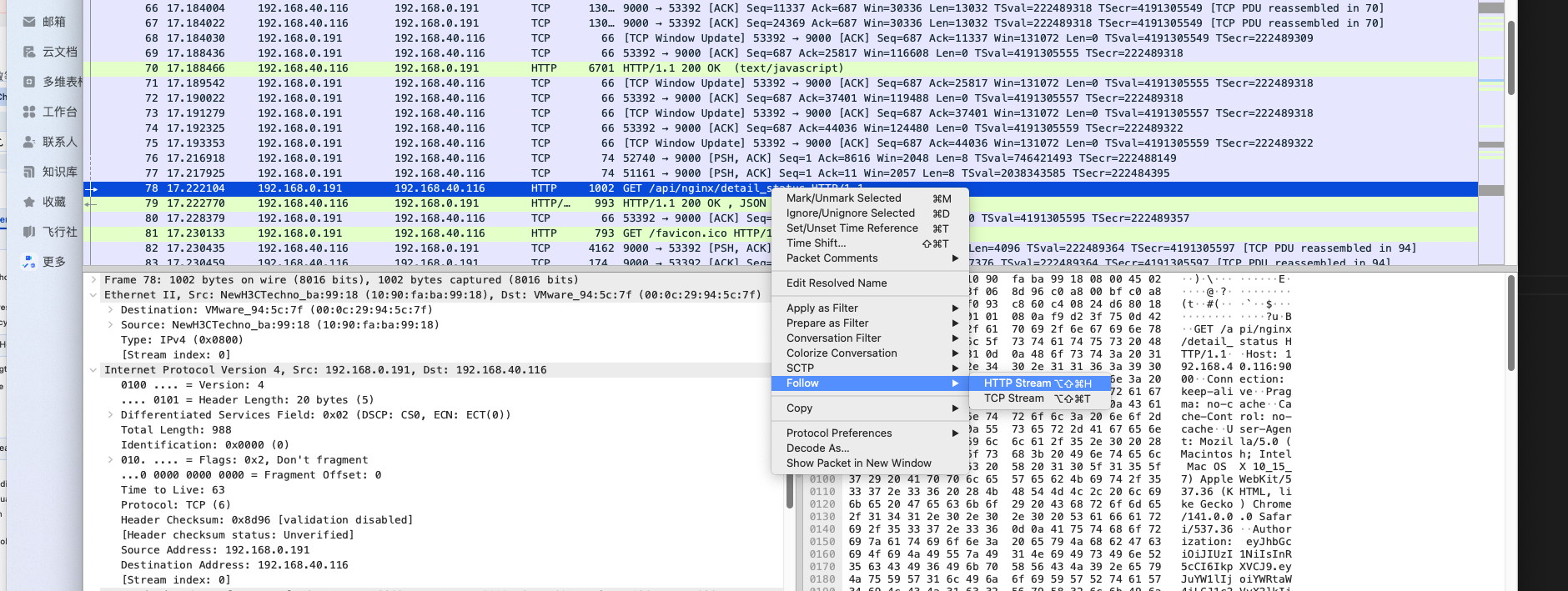
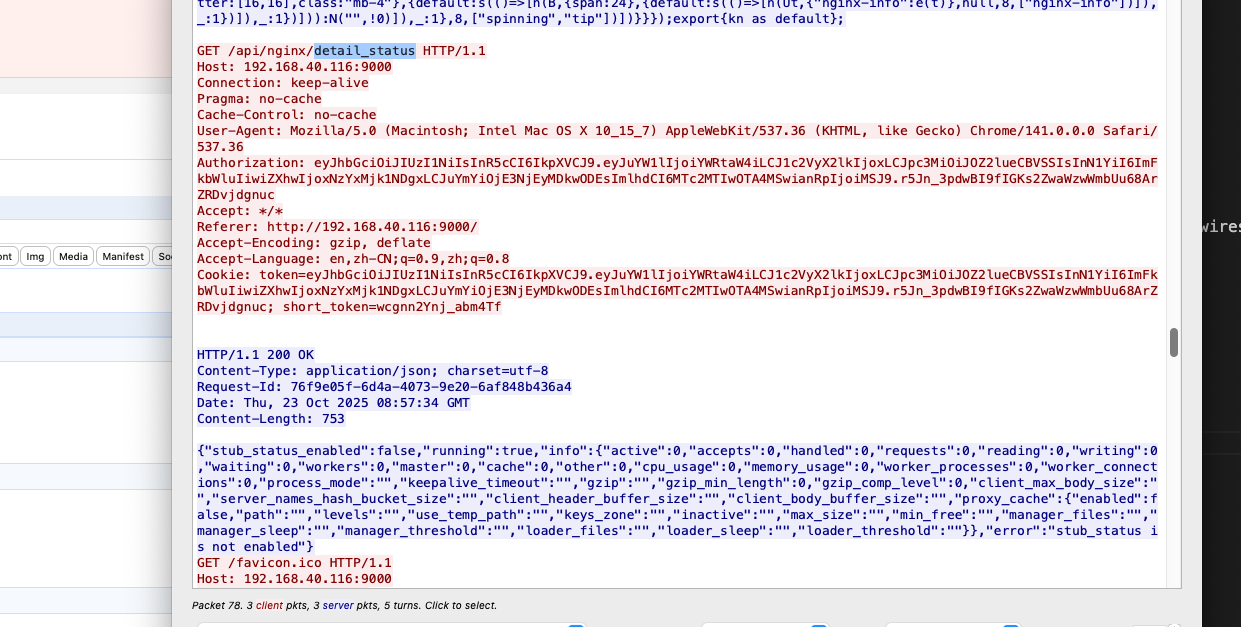
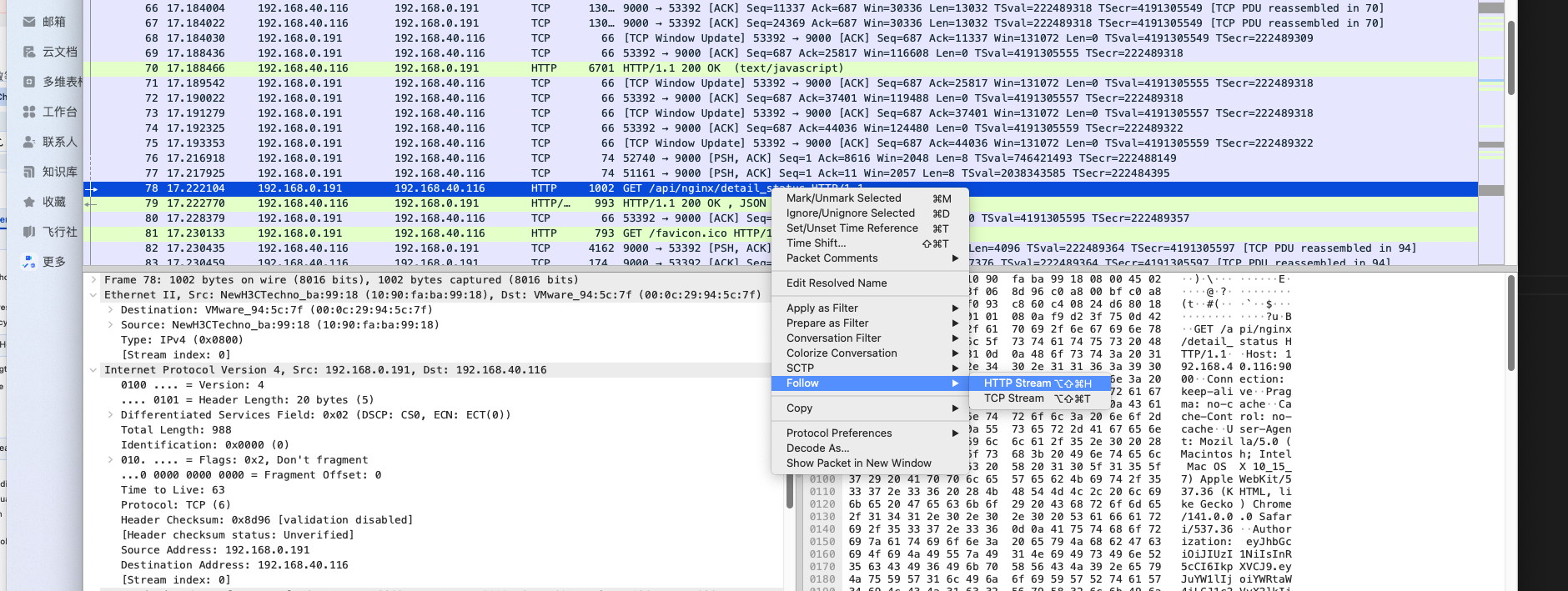
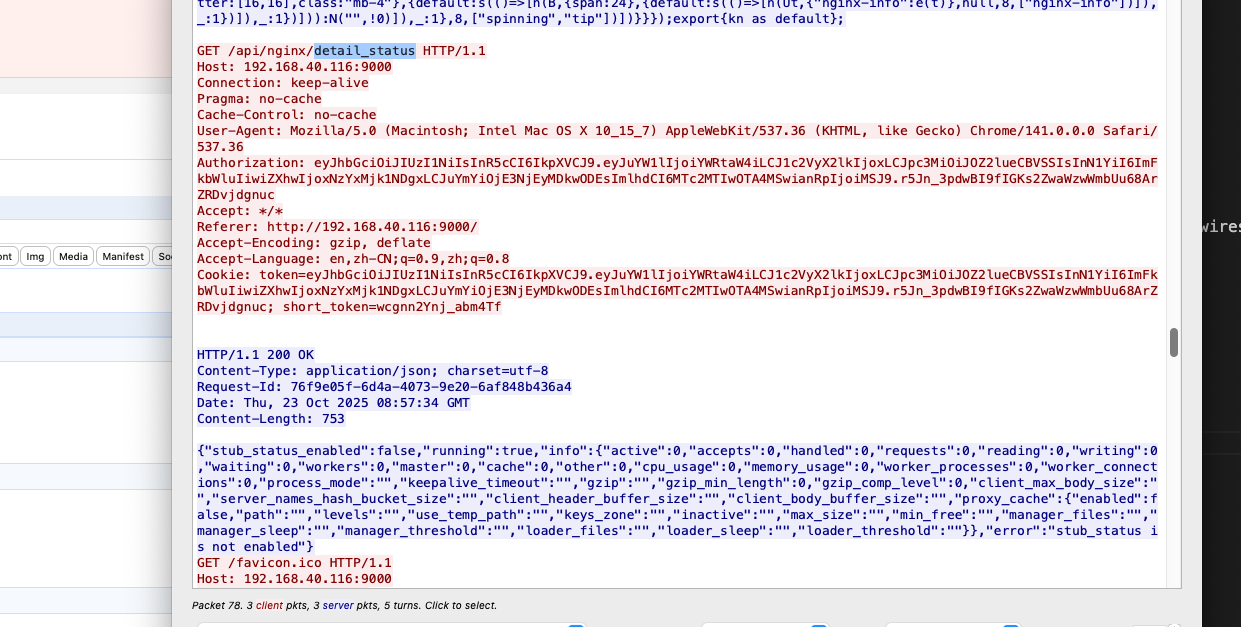
将其 拉入到 wireshark 进行分析
sudo ln -s /Applications/Wireshark.app/Contents/MacOS/Wireshark /usr/local/bin/wireshark
wireshark a.cap
也可以将 a.cap 文件拉入到 wireshark 中进行查看
sudo tcpdump ‘port 18080’ -w 73_3.cap -i any
scp admin@192.168.40.73:/home/admin/73_3.cap ./